Hello everbody,
Proudly writing this from my new Surface Laptop 7 with Copilot 😀
Note: (I know guys, the Windows LAPS is available for a while now and there are numerous articles on the internet already how to configure it. However, I think all of you will be interested in part 2 – Creating a Power App that retrieves the LAPS password from the device you put in.)
Today, I am going to show you how you can enable and configure Windows LAPS in your tenant if you administer your devices with Microsoft Intune.
What is Windows LAPS?
Windows Local Administrator Password Solution (Windows LAPS) is a Windows feature that automatically manages and backs up the password of a local administrator account on your Microsoft Entra joined or Windows Server Active Directory-joined devices. You also can use Windows LAPS to automatically manage and back up the Directory Services Restore Mode (DSRM) account password on your Windows Server Active Directory domain controllers. An authorized administrator can retrieve the DSRM password and use it.
Windows LAPS with Microsoft Entra ID and Microsoft Intune support is now in General Availability as of October 23 2023.
Requirements
- Microsoft Intune
- Microsoft Entra ID Free or higher license
- Entra ID Joined and Intune managed device
Supported platforms
Windows LAPS is now available on the following OS platforms with the specified update or later installed:
- Windows 11 22H2 – April 11 2023 Update
- Windows 11 21H2 – April 11 2023 Update
- Windows 10 – April 11 2023 Update
- Windows Server 2022 – April 11 2023 Update
- Windows Server 2019 – April 11 2023 Update
All supported editions of the above platforms have been updated with Windows LAPS, including LTSC editions. The introduction of the Windows LAPS feature doesn’t modify in any way whatsoever the standard Microsoft product lifecycle policies.
Enable Windows LAPS in Entra ID
- Go to Microsoft Entra admin center and sign in with your credentials
- Go to Devices –> Overview –> Device Settings
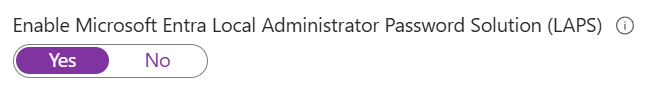
- Scroll down to “Local Administrator Password Settings” and look for “Enable Microsoft Entra Local Administrator Password Solution (LAPS)”
- Make sure that this settings is set to “Yes”
Windows LAPS is now enabled in your tenant.
Configure Windows LAPS in Microsoft Intune
- Go to Microsoft Intune admin center and sign in with your credentials
- Go to Endpoint Security –> Account Protection
- Create new policy. Select platform “Windows 10 and later” and profile “Local Administrator Password Solution (Windows LAPS)”
- Give your profile a name like “Windows LAPS Configuration”
- Configure the settings per your requirements. Mine are configured in below:
- Backup Directory: Backup the password to Azure AD only
- Password Age Days: 7 (Minimum for Entra ID)
- Administrator Account Name: LAPSWKSAdmin
- Password Complexity: Large letters + small letters + numbers + special characters
- Password Length: 14
- Post Authentication Actions: Reset the password and logoff the managed account
- Post Authentication Reset Delay: 1
- Configure scope tags if you have them
- Assign the profile to a group of devices or to all of them
The Windows LAPS policy has been created now.
Option 1: Create new administrator account
For successfully managing the local admin account and it password with Windows LAPS, we have to create a new administrator account with the same name as we specified in the earlier created Windows LAPS policy.
- Go to Microsoft Intune admin center and sign in with your credentials
- Go to Devices –> Configuration –> Create –> New policy
- Select platform “Windows 10 and later” and profile “Templates”
- Select “Custom”
- Give your profile a name like “Windows LAPS Account”
- Select the Settings tab and press “Add”:
- OMA-URI: ./Device/Vendor/MSFT/Accounts/Users/LAPSWKSAdmin/Password
- Data Type: String
- Value: Generate a strong password for the account
- Add another OMA-URI:
- OMA-URI: ./Device/Vendor/MSFT/Accounts/Users/LAPSWKSAdmin/LocalUserGroup
- Data Type: Integer
- Value: 2
- Assign the profile to a group of devices or to all of them
Option 2: Enable and rename the built-in administrator account
For successfully managing the local admin account and it password with Windows LAPS, we have to create one policy to enable the built-in administrator account and rename it to the account name specified in the Windows LAPS policy. This is not recommended by Microsoft.
- Go to Microsoft Intune admin center and sign in with your credentials
- Go to Devices –> Configuration –> Create –> New policy
- Select platform “Windows 10 and later” and profile “Settings catalog”
- Give your profile a name like “Enable and rename LAPS”
- Configure the following settings in Local Policies Security Options:
- Accounts Enable Administrator Account Status: Enable
- Accounts Rename Administrator Account: LAPSWKSAdmin
- Configure scope tags if you have them
- Assign the profile to a group of devices or to all of them
The policy has been created now.
View Windows LAPS passwords
The following roles and permissions can view LAPS attributes:
- Global Administrator
- Intune Administrator
- Cloud Device Administrator
- Custom role
In some cases, the default roles are giving too many permissions. A solution is to create a custom role that only reads the LAPS attributes.
- Custom role:
- Go to Microsoft Entra admin center and sign in with your credentials
- Go to Identity –> Show more –> Roles & Admins
- Press “New custom role”
- Give your role a name like “LAPS Password Reader”
- Assign the following permissions:
- Permission: microsoft.directory/deviceLocalCredentials/password/read
- Permission: microsoft.directory/deviceLocalCredentials/standard/read
- Review and create the role
- Intune role:
- Go to Microsoft Intune admin center and sign in with your credentials
- Go to Tenant Administration –> All roles
- Press “Create” –> “Intune role”
- Give your custom role a name like “LAPS Password Reader”
- Assign the following permissions:
- Managed Devices: Read
- Organization: Read
- Remote Tasks: Rotate local admin password
- Review and create the role
- Press on the newly created role and look for “Assignments”
- Press “Assign”
- Give your assignment a name like “LAPS Password Reader Assignment”
- In the “Admin Groups” select a group that contains the accounts that should be able to view and rotate the LAPS password
- In the “Scope Groups” select a group of devices or all devices you want to view and rotate the LAPS password from
- Review and create the assignment
How to view:
- Go to Microsoft Intune admin center and sign in with your credentials
- Go to Devices –> All Devices
- Go to the device you want to see the password of and look for “Local Admin Password”
- Press “Show local administrator password”

You have successfully configured Windows LAPS for your Intune managed devices.
In part 2, I am going to explain how you can retrieve LAPS password through a Power App by using Power Automate to build the workflow and the Power App for displaying the LAPS attributes.
Stay tuned! 🙂
